No SSH and HTTP connections to OPNsense WAN interface via IPv6
A few days ago I noticed that I could not use my OPNsense firewall as a SSH jump host to my other servers. I’m not sure how long this issue has existed, or if it has always existed, but since I’ve had IPv6 connectivity after a long time of IPv4-only internet, I could definitely feel the consequences.
While ssh root@opnsense worked perfectly, ssh -6 root@opnsense failed with a timeout. Verbose output of the ssh command showed that the client was trying to access the correct IPv6 address of my firewall, but obviously it did not receive any response.
“Hah! Easy fix!” I thought while logging into my firewall’s web interface and trying to find the WAN interface rules. But the rules were correctly: They applied to the correct interfaces wich the correct ports and were active. I could even see SSH connections “pass” through the WAN interface via the firewall log viewer. The firewall rules seemed to be okay.
But what about the route back to my client? Was the default gateway okay? Did IPv6 work from my firewall to the internet? Yes, it did. No problems there.
I was almost about to give up when I found the following (german) blog article: https://www.andysblog.de/opnsense-zugriff-auf-das-web-interface-ueber-wan
The author states that checking the disable reply-to checkbox in the corresponding firewall rules of the WAN interface made his IPv6 connections work. Although, he mentions that he cannot explain why that is the case.
Indeed, “disabling reply-to” worked in my case. I checked the box for HTTP and SSH on my WAN interface. You can find the location of the check box in this screenshot:
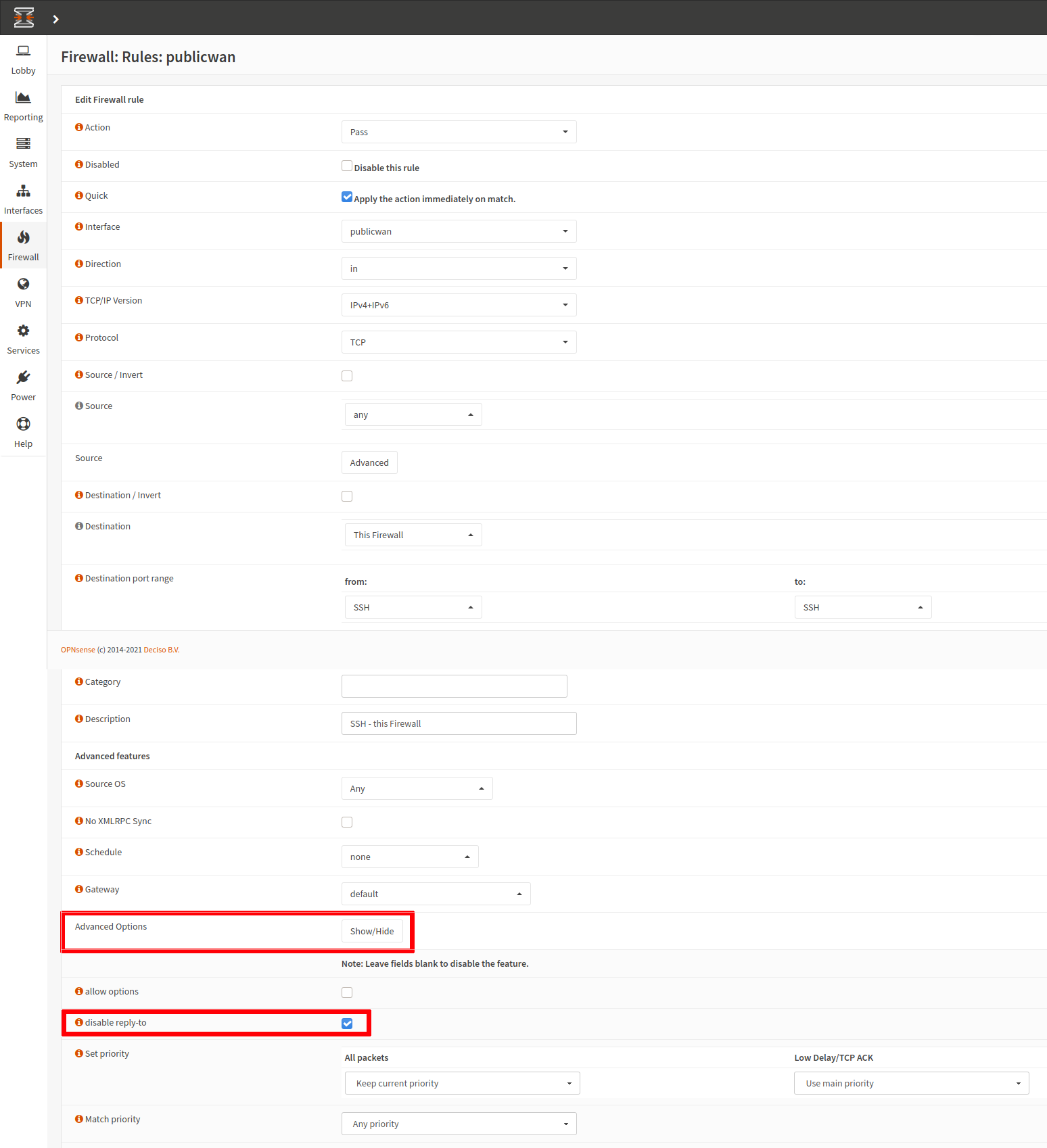
settings to be changed in the rule settings, e.g. of the SSH-allow-rule
There is also a thread on the OPNsense forums: https://forum.opnsense.org/index.php?topic=15900.0


